FROM THE TEAMiuvo Blog & News
Insights, ideas, and field notes from the iuvonauts — written for the people making IT decisions every day.
Filter By Topic
IT Management
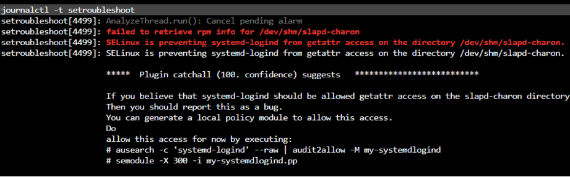
SELinux: Why it's time to stop turning it off
Apr 26, 2022 9:30:00 AM
IT Management
Enhance Productivity through Core Values
Apr 5, 2022 9:30:00 AM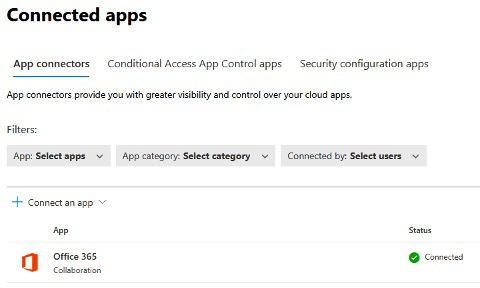
IT Management
Protecting Your Data with Microsoft Sensitivity Labels
Mar 29, 2022 9:30:00 AM
IT Management
Three Tips for Successfully Navigating the Great Resignation
Mar 22, 2022 9:37:47 AM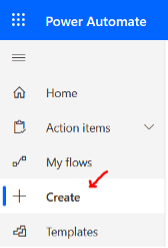
Cloud
How to Move Files in Microsoft Sharepoint Using Power Automate
Mar 15, 2022 9:30:00 AM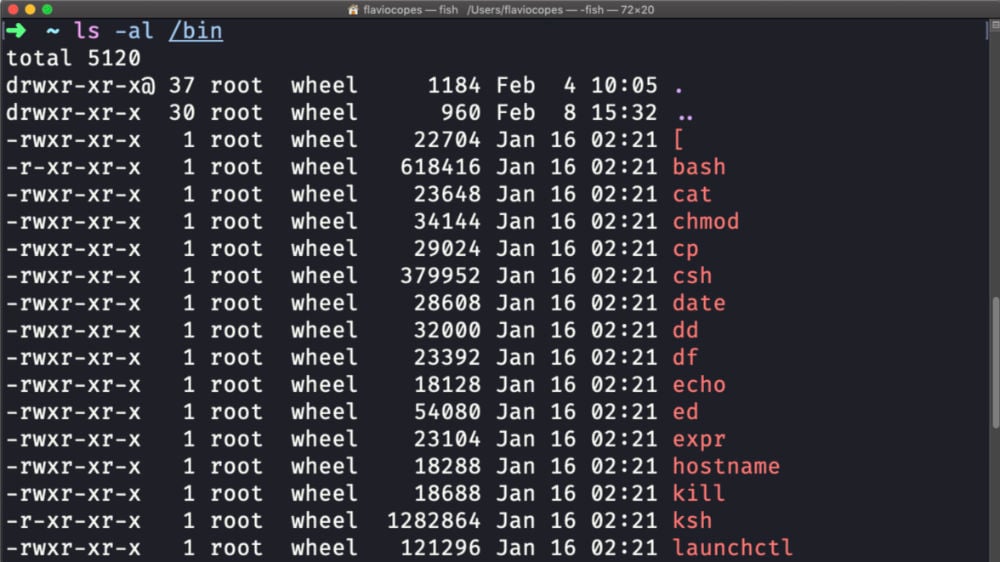
Cloud
How To Calculate UNIX File Permissions
Mar 1, 2022 9:30:00 AM
IT Management
Business Empowerment: Where Information Technology Intersects Growth
Feb 22, 2022 9:30:00 AM
Cloud
SSSD Linux Active Directory Authentication: Joining a Domain Without VPN
Feb 15, 2022 9:30:00 AM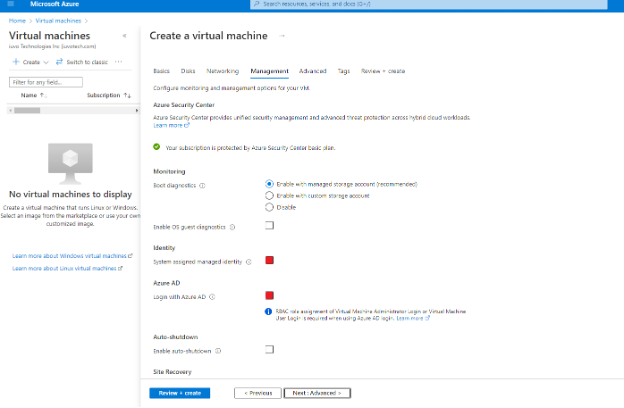
Cloud
Azure AD Authentication to Azure VM
Feb 8, 2022 9:30:00 AMNo posts on this page match your search.
Want More iuvo Insights?
Subscribe and get fresh thinking from our iuvonauts delivered to your inbox.
Subscribe to the Blog