Cyber threats continue to evolve taking on new forms and techniques. One of the latest trends in cybercrime is "quishing," a method that leverages QR codes to deceive and manipulate unsuspecting victims. At iuvo, we understand the importance of staying ahead of such threats. In this blog we will discuss how businesses can protect themselves.
Understanding Quishing
Quishing, or QR code phishing, is a method in which cybercriminals trick users into scanning QR codes that lead them to malicious websites. These sites could potentially install malware, solicit sensitive personal and financial information, or hijack user credentials.
How Quishing Attacks Work
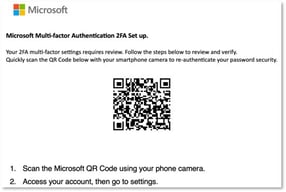
The attacker introduces you to a QR code through something like emails, physical stickers, or direct messages. These codes, when scanned, redirect you to a website or application. The QR codes are designed to appear harmless and legitimate and will often mimic popular brands or companies. They are strategically placed in areas where you are likely to encounter them, like on posters, flyers, or even in public restrooms. The intention is to get you to scan the code out of curiosity or convenience.
Once you scan the infected QR code, you then land on a website that is designed to imitate trusted sites, ultimately tricking you into sharing your personal information or downloading malicious software. These sketchy websites often replicate the look and feel of legitimate websites that you’ve visited, making it difficult for you to know the difference. The attackers go as far as copying logos, fonts, and website layouts, to create a convincing facade. Once on the website, you might be prompted to enter your login credentials, credit card information, or other sensitive data, completely unaware that you are handing it right over to the cybercriminals.
When you interact with the sketchy site, the attacker is then able to harvest your shared data, paving the way for potential financial fraud, identity theft, or business data breaches. Your stolen information can be used for things like making unauthorized transactions, creating fake identities, or your information can even be sold on the dark web.
The Rise of Quishing
With the COVID-19 pandemic, the use of QR codes skyrocketed as businesses looked for low-contact means of interaction with their customers, be it for menus, payments, or information sharing. While convenient, this growing familiarity with QR codes created fertile ground for cybercriminals to launch quishing attacks.
From phony parking meter QR codes to deceptive emails mimicking legitimate companies, quishing is becoming a growing problem. While individual consumers have been the primary targets, businesses and their employees aren't immune. Company email accounts are now targets for cybercriminals, given the wealth of data they often contain.
Quishing Scams Impact on Businesses
Beyond the immediate and obvious financial losses that can result from fraudulent transactions, a successful quishing attack can lead to unauthorized access to your business’ sensitive data, including proprietary information, customer details and employee records.
This breach can damage your company's reputation, weakening trust among your clients and your potential customers. As news of the breach spreads (and it always does), your customers may become hesitant to engage with your business for fear that their personal information may be compromised. You could experience decreased sales, customer churn and difficulty acquiring new customers because of this loss of trust.
As if the reputational damage wasn’t enough, your business could also face the challenge that comes with having to allocate significant time and resources to address and rectify a quishing attack. Your IT team must diligently investigate the full extent of the attack, identify and patch vulnerabilities, and implement measures to prevent future attacks.
Productivity and growth can be hindered thanks to the distraction caused by dealing with a quishing attack which can divert attention from your main business activities. Instead of focusing on strategic initiatives and driving innovation, your team may be consumed by the task of resolving the breach leading to missed opportunities, delayed projects, and reduced overall efficiency.
In some cases, businesses that fail to protect their data may face regulatory penalties or lawsuits, further compounding the financial strain.
Protecting Your Business from Quishing Attacks
Protection against quishing revolves around a combination of user education and robust cybersecurity measures. Below we’ve listed some tips to protect your business.
Educating the Workforce
- Make sure to always verify the source of a QR code before scanning, especially if it's received via email or message.
- If a QR code is received from a known contact, validate its authenticity through a separate communication channel.
- Be aware of the typical indicators of phishing, such as urgency or emotional triggers.
- Before engaging with content from a scanned QR code, check the URL for authenticity. Look for HTTPS, check for typos, and avoid unfamiliar or shortened links.
- If a scanned QR code redirects you to a website requesting your personal data, credentials, or payment, approach with extreme caution.
- Regularly change your passwords and avoid reusing them across different accounts.
Implementing Cybersecurity Measures
- Regulate which applications and sites can be accessed.
- Make sure emails containing malicious content are filtered out with anti-spam filters.
- Establish strong email security policies to prevent phishing attempts.
- Mandate strong, unique passwords and frequent changes for all team members in your business.
- Use Multifactor Authentication (MFA) as an added layer of security to verify user identities.
- Implement antimalware software that actively scans and removes malicious software.
- Use a threat intelligence service to stay updated with the latest threat intelligence to proactively fight potential threats.
Quishing is just one of the many tactics cybercriminals are using to exploit unsuspecting victims. By staying informed and proactive, you can protect your business against such threats. If you're concerned about quishing or any other cybersecurity threat, reach out to our expert team for guidance and support.
Related Content:
- Backup and Recovery Testing (iuvotech.com)
- Protecting Your Business: The Cyber Risks of Social Media (iuvotech.com)
- Backup Best Practices (iuvotech.com)
- Best Practices for File Safety (iuvotech.com)



.png)
.png)
.png)