FROM THE TEAMiuvo Blog & News
Insights, ideas, and field notes from the iuvonauts — written for the people making IT decisions every day.
Filter By Topic

Process
The Art of Vendor Escalation Management
Jun 13, 2024 9:44:32 AM
Process
The business impacts of Revenue Operations
Feb 14, 2023 9:30:00 AM
Process
How OpenAI's ChatGPT is Revolutionizing the Technology World
Jan 17, 2023 9:30:00 AM
Process
Getting (Digitally) Organized in the New Year
Jan 10, 2023 9:30:00 AM
IT Management
Three Tips for Successfully Navigating the Great Resignation
Mar 22, 2022 9:37:47 AM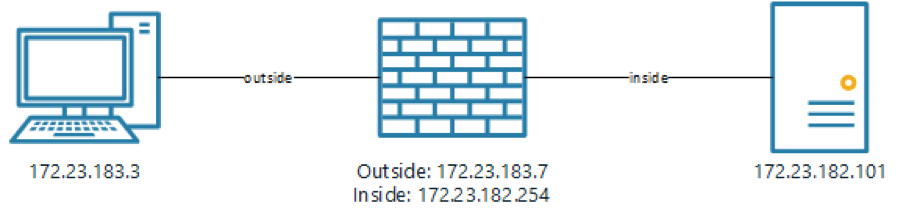
IT Management
Troubleshooting a CISCO ASA with ASDM
Nov 22, 2021 7:02:53 PM
Cloud
The Cost of On-Premises IT Infrastructure
Mar 23, 2021 9:30:00 AM
IT Management
Active Directory CIFS (Samba) w/ CentOS/Red Hat Enterprise Linux 8
Feb 16, 2021 9:30:00 AM
IT Management
2021 Trends to Watch Out For
Feb 9, 2021 9:30:00 AMNo posts on this page match your search.
Want More iuvo Insights?
Subscribe and get fresh thinking from our iuvonauts delivered to your inbox.
Subscribe to the Blog