Companies are now increasingly reliant on technology and the internet to conduct their business. With phishing attacks growing in sophistication, businesses must now utilize advanced technology and tools to defend themselves against attacks.
AiTM Phishing Attacks
Phishing attacks are a growing concern for businesses. In fact, according to an article from Microsoft, phishing is one of the most common techniques attackers are using in their attempts to gain initial access to a company. With phishing attacks, users are tricked into revealing sensitive information, such as passwords or personal identification numbers. We are now seeing that advanced threats like Adversary-in-the-middle (AiTM) are an even greater risk to businesses but with the use of Microsoft Technology, it is possible for businesses defend themselves from these attacks.
How AiTM phishing attacks work
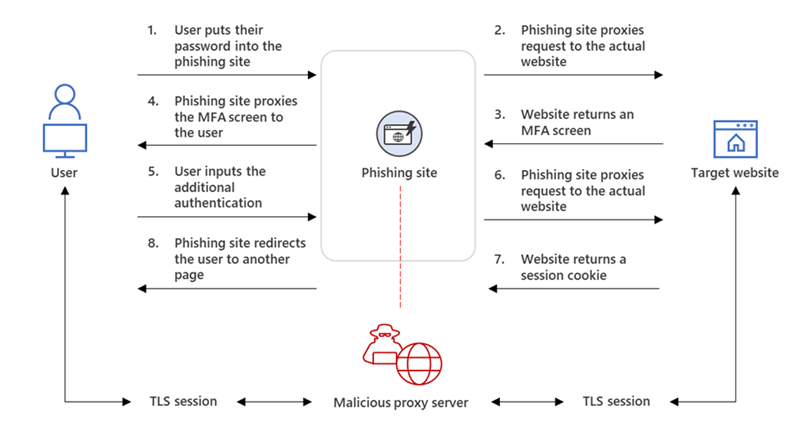
AiTM phishing allows the attackers to intercept communications between two parties, such as a user and a legitimate website, to steal sensitive information. Below we have outlined in detail how an AiTM phishing attack works.
- The user accesses the target website by typing in the website's URL or by clicking on a link to the website through a phishing email.
- The attacker then intercepts the user's request and sends it to a phishing website that looks just like the legitimate website but is in fact controlled by the attacker.
- The user is then redirected to the phishing website and is prompted to enter sensitive information like their login credentials.
- The attacker is then able to capture the user's information as it is entered on the phishing website. Additionally, the attacker gathers the session cookie issued by Microsoft which allows them to ultimately bypass multi factor authentication (MFA).
- With the stolen information, the attacker can then access the user's account for a variety of malicious purposes, such as identity theft, financial fraud, or even espionage.
This graphic from Microsoft illustrates this process:
Defending Against Phishing Attacks With Microsoft
By utilizing Microsoft’s wide range of tools and technologies, such as Microsoft 365 Defender, organizations can better protect themselves against AiTM/MFA phishing attacks. Here are some effective ways to protect against these advanced phishing attacks using Microsoft technology:
Use Multi-Factor Authentication (MFA)
Don't discount MFA! While AiTM phishing attacks have devised a way to bypass MFA, it is still considered one of the most effective ways to protect against traditional phishing attacks. When organizations enable MFA, it makes it much more difficult for attackers to gain access to sensitive information, even if they have obtained a user’s password. This is because MFA requires users to provide more than one form of authentication, such as a password and a one-time code sent to their phone, to gain access to an account.
Microsoft provides a range of MFA technologies, such as Azure Multi-Factor Authentication and Microsoft Authenticator, which can be used to secure both personal and corporate accounts. According to Microsoft, organizations can support their MFA implementation to be resistant to phishing by utilizing solutions such as Windows Hello for Business that support Fast ID Online (FIDO) v2.0 and certificate-based authentication.
Implement Conditional Access Policies
GitHub describes Conditional Access policies as if-then statements, if a user wants to access a resource, then they must complete an action. Conditional Access policies are an important component to building an organization's defense against AiTM phishing attacks because they allow administrators to set policies that control access to resources based on certain criteria, such as the user's location or the type of device they are using. With Azure AD Conditional Access organizations can ensure access to sensitive resources is only granted to users who meet very specific criteria, making it much more difficult for attackers to bypass MFA authentication mechanisms.
Use Advanced Threat Protection
Microsoft's Advanced Threat Protection (ATP) provides a range of tools and technologies to help organizations protect against advanced persistent threats. As defined by Nakivo, "ATP is a cloud-based filtering service for cyberthreat prevention and detection that uses machine learning algorithms to detect and respond to threats in real-time, including phishing attacks."
In addition, the ATP tool also protects organizations against other threats, such as ransomware and zero-day attacks. ATP’s ability to integrate with Microsoft 365 services such as OneDrive, SharePoint Online, and Exchange Online make it an essential tool for organizations that are looking to protect against these advanced threats.
Educate Users on Phishing Awareness
Education is a key component to defending against these threats. Users within an organization need to be educated on how to recognize phishing attacks, in addition to being made aware of the importance of using security technologies and MFA. Thanks to Microsoft’s range of training materials and resources, organizations can help to educate their users.
The Microsoft Security Awareness Toolkit is one such resource. This toolkit provides organizations with quick and convenient training materials such as videos, interactive courses, posters, and infographics to help educate and empower their employees.
Although AiTM phishing attacks are not a new threat to organizations, attackers are evolving rapidly, requiring advanced tools and technologies to protect against them. Using Microsoft's MFA technologies, Conditional Access Policies, Advanced Threat Protection, and educating organization users on phishing awareness, can significantly reduce the risk of falling victim to these advanced phishing attacks.
If you would like assistance in ensuring your company's data is protected, please contact us and we would be happy to help.

-1.png)
-1.png?width=600&height=401&name=Untitled%20design%20(5)-1.png)
.png)
.png)
.png)