FROM THE TEAMiuvo Blog & News
Insights, ideas, and field notes from the iuvonauts — written for the people making IT decisions every day.
Filter By Topic
.png)
IT Management
What do you need from your IT Service Provider?
Nov 26, 2024 11:00:00 AM
IT Management
What is Intune Company Portal? Definition and Application Guide
Sep 14, 2021 9:30:00 AM
Cloud
How to Access and Use My Company's SharePoint Documents
Aug 10, 2021 11:30:00 AM
IT Management
Common Computer Issues For Remote Workers & How To Troubleshoot Them
Apr 13, 2021 9:30:00 AM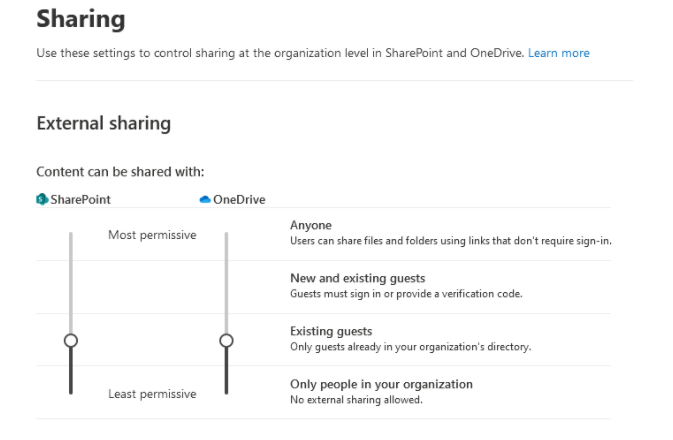
IT Management
Conditional Access Policies: Require MFA For Guests In o365 Tenant
Jan 19, 2021 9:30:00 AM
Disaster Recovery
Best Practices for File Safety
Jun 16, 2020 9:30:00 AM
IT Management
How To Set Up the Google and Microsoft MFA
May 26, 2020 9:30:00 AM
Cloud
Managed Services – What It Is And How We Are Different
Jan 14, 2020 9:30:00 AM
IT Management
Human Firewalls: What They Are And Why They're Important
Jul 23, 2019 9:30:00 AMNo posts on this page match your search.
Want More iuvo Insights?
Subscribe and get fresh thinking from our iuvonauts delivered to your inbox.
Subscribe to the Blog