FROM THE TEAMiuvo Blog & News
Insights, ideas, and field notes from the iuvonauts — written for the people making IT decisions every day.
Filter By Topic

IT Management
Surprisingly Universal Things Learned from Software Development
Aug 27, 2019 9:30:00 AM
IT Management
How Do You Measure Success?
Aug 6, 2019 9:30:00 AM
IT Management
Startups: Why IT Is Important & How iuvo Technologies Can Help With Growth
Jul 30, 2019 9:30:00 AM
IT Management
Human Firewalls: What They Are And Why They're Important
Jul 23, 2019 9:30:00 AM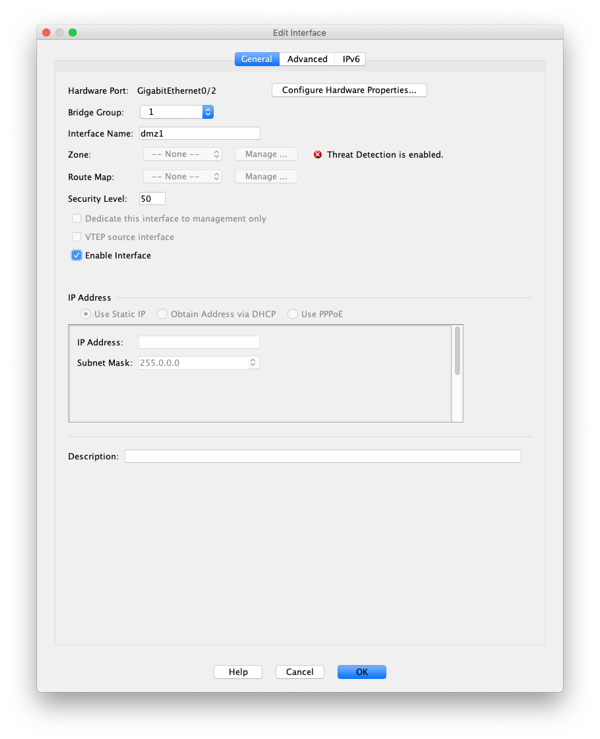
IT Management
Port Forwarding with CISCO ASA and ASDM
Jul 16, 2019 9:30:00 AM
IT Management
Gradual Escalation in Vendor Escalation Management
May 28, 2019 10:00:00 AM
IT Management
Documentation in Vendor Escalation
May 7, 2019 6:24:54 PM
Process
The Importance of Being Available
Apr 9, 2019 3:03:13 PM
IT Management
A Guide to Rule-Based vs. Role-Based Access Control: What are the Differences?
Mar 28, 2019 7:00:13 PMNo posts on this page match your search.
Want More iuvo Insights?
Subscribe and get fresh thinking from our iuvonauts delivered to your inbox.
Subscribe to the Blog